Blog
Insights for MSP Operations Leaders
Frameworks, strategies, and lessons from consulting with and coaching MSP operations teams.
Join 1,900+ MSP leaders. Weekly delivery.
Latest
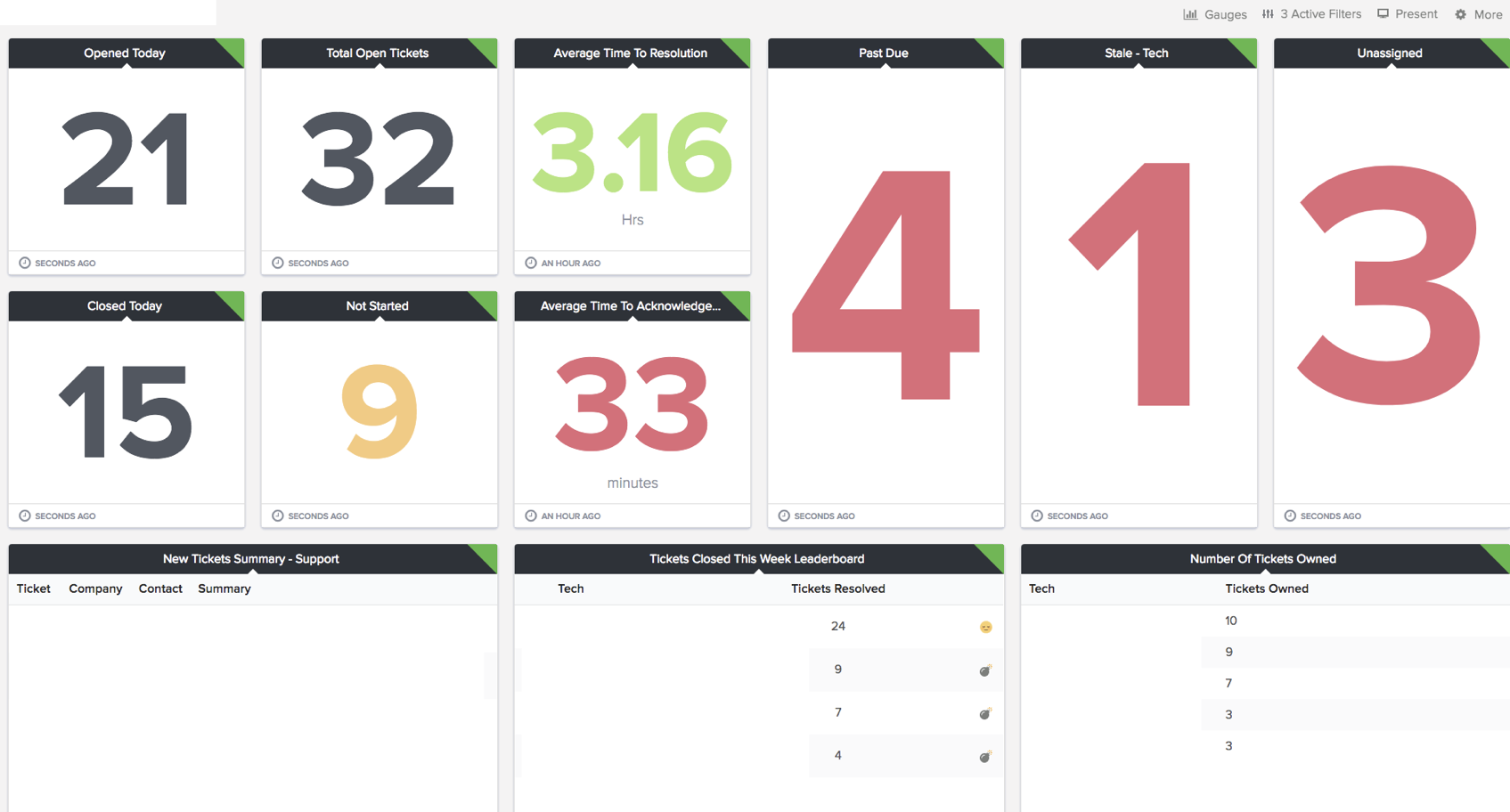
Dispatch Data for Amazing Service Delivery
How a well-built BrightGauge dispatch board helps MSPs manage the service queue by exception, keep tickets moving, and deliver a five-star client experience.
Read article
How to Calculate Your MSP's Cost Per Ticket
Learn how to calculate your MSP's cost per ticket with a simple formula, industry benchmarks from MetricNet, and three steps to drive the number down.

How to Manage After-Hours Support at Your MSP
Compare five methods for handling after-hours support at your MSP, from shared inboxes to outsourced help desks, with honest pros and cons for each approach.

What McDonald's Can Teach MSPs About Service Delivery
How lean principles from McDonald's Speedee System apply to MSP service delivery. Strip complexity, eliminate waste, and build efficiency into your IT operations.
Do I Need to Hire More Staff?
When service teams face pressure to improve, the answer isn't always more people. Before you hire, eliminate the inefficiency hiding in your operation.

How MSPs Must Adapt to WFH
The pandemic changed work forever. MSPs that embrace remote work gain recruitment advantages and reduced overhead. Those resisting face attrition.

MSP Service Metrics You Need
Managing IT service delivery at scale requires data. Here are the essential service metrics every MSP should track, with industry benchmarks.

Using MSP Business Metrics
Having objective measurements of MSP performance is crucial. Here are the business metrics that matter most, with targets and how to use them.
Is Tracking Time an Outdated Approach?
Time tracking in MSPs is controversial. It's not the villain you think — the problem is the tools, not the practice.

The Two Pizza Rule
Why the two pizza team makes your company more productive. Smaller teams drive accountability, communication, and cost efficiency.

MSP Documentation Systems
Documentation is critical for effective IT support. Here's a comparison of the leading MSP documentation platforms — from IT Glue to Hudu.

The "Best" MSP Pricing Model
Comparing fixed fee, tiered, per device, and per user pricing models for MSPs. Why per-user all-in seat pricing wins.
Windows 7 Support Is Ending, What Are You Doing About It?
Microsoft ended Windows 7 support. Here's how MSPs should plan the transition — from client communication to hardware scoping to upgrade proposals.
Why Personality Tests Are Useless
Myers-Briggs is fun but scientifically unreliable. DISC behavioral profiling is different — it's based in science and the results are shockingly accurate.

What to Do When a Client's IT Is a Total Mess
New client onboarding with a chaotic IT environment? Here's how to assess, standardize, and clean up the mess without losing your mind.

How Measuring Customer Satisfaction Impacts Your Business
Customer satisfaction scoring isn't just a nice-to-have. It directly impacts retention, referrals, and revenue. Here's how to implement it.

Managed Services Metrics Service Managers Should Focus On
Service managers need a focused set of metrics to drive performance. Here are the ones that actually move the needle.

Getting Your Techs to Enter Time
Time entry is the bane of every MSP tech's existence. Here's how to make it stick — with practical strategies that actually work.

How Customer Surveys Create Better Customer Service
Customer surveys aren't just feedback tools — they're service improvement engines. Here's how to use them to drive real change in your MSP.

5 Key Ingredients to a Successful Team
Building a high-performing team isn't magic. It comes down to five fundamentals that most managers overlook.
Improve Your Project Management Practices — Conducting a Project Kickoff and Close
The kickoff and close are the most neglected parts of project management. Here's how to do them right and improve your project outcomes.
How MSPs Achieve Great Service Level Agreements
SLAs are more than a contract checkbox. Here's how to build, measure, and deliver SLAs that actually mean something to your clients.
5 Simple Ways to Measure Your Project Management Maturity
Most MSPs know they need better project management. Here are 5 practical ways to measure where you are and what to improve.

A Modern Approach to Managing Teams
Traditional management styles are failing modern teams. Here's a framework for managing IT teams that drives engagement and results.

The Panama Papers — How Were They Hacked?
The Panama Papers breach exposed 2.6TB of data. Here's a technical breakdown of how it happened and what it means for IT security.

Technical Debt Creating Risk?
Technical debt isn't just a developer problem. It creates real security and operational risk in managed IT environments.

Control Employee Turnover to Save Money
Employee turnover costs 80-120% of annual salary to replace. Here's how to reduce churn and keep your best people.
Free eBook
14 Essential SOPs Every MSP Should Have
Your blueprint to building a procedure-based culture. These are the exact SOPs that high-performing MSPs use to run service delivery, handle escalations, onboard clients, and keep their teams accountable.
- 14 SOPs to cut ticket time by 50% or more
- Covers service delivery, projects, and account management
- Downloaded by 144+ MSP leaders
Free. No spam. Unsubscribe anytime.